You wake up to a seemingly impossible support ticket. A prospective enterprise client from Milan - or perhaps a loyal reader from Tokyo - has reached out with a frustrating message: "I can't access your website." They attach a screenshot. It’s a harsh, unbranded browser error. A timeout. Or worse, a stark governmental warning page.
You immediately check your analytics and server health. Everything on your dashboard is glowing green. You don't host pirated movies, you don't distribute malware, and your business is strictly legitimate. You sell B2B software, run a local news blog, or operate a boutique e-commerce store.
So, why is a perfectly legal, non-controversial website suddenly facing a digital embargo in specific regions of the world?
The contemporary internet is often romanticized as a borderless network, but the reality is a highly fragmented infrastructure defined by aggressive security algorithms, localized technical failures, and rigid legal boundaries.
If your website is experiencing unexplained regional blocking, you are likely the victim of what we call "non-punitive digital exclusion." Here is the exhaustive breakdown of why this happens, the invisible mechanisms at play, and how you can diagnose and resolve the issue.
Table of contents
- 1. The Crossfire of Shared Infrastructure (IP Contamination)
- 2. Regulatory Geofencing and the Crushing Cost of Compliance
- 3. The Protocol Arms Race: How Upgrading Security Gets You Blocked
- 4. Overzealous Web Application Firewalls (WAF) and Anomaly Scoring
- 5. Invisible Glitches: BGP Leaks and SSL Misconfigurations
- How to Diagnose and Resolve Non-Punitive Regional Blocks
1. The Crossfire of Shared Infrastructure (IP Contamination)
The architectural design of the modern web relies heavily on resource pooling. When you use a Content Delivery Network (CDN) or a shared hosting provider, your domain does not get a solitary, isolated IP address. Instead, your site shares an IP address with hundreds, sometimes thousands, of entirely unrelated websites.
While this makes hosting affordable and fast, it creates a profound vulnerability.
Imagine a governmental regulatory body - like Italy’s communications authority, AGCOM - deploying an automated system to block illegal live streaming of football matches. Their system, known as "Piracy Shield," empowers copyright holders to demand ISPs block specific IP addresses within 30 minutes.
Because illicit operators frequently lease generic CDN infrastructure or dynamically rotating IP addresses, authorities often end up blacklisting a shared node. When that happens, your legitimate business, which simply happened to be assigned the same IP address by your CDN provider, is instantly erased from that country’s internet.
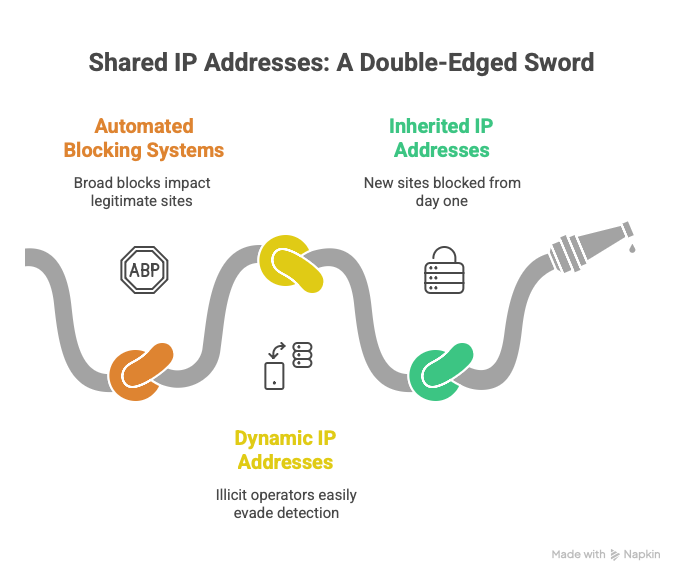
In February 2024, a single block directed at a Cloudflare IP address by the Italian government accidentally rendered tens of thousands of innocent websites completely inaccessible to Italian users for hours. Furthermore, if you lease a new server and inherit an IP address previously "polluted" by a malicious tenant, you will find your site blocked from day one, entirely unaware of the historical baggage attached to your network routing.
2. Regulatory Geofencing and the Crushing Cost of Compliance
Sometimes, the block isn't coming from an external firewall; it’s being enforced by your own hosting infrastructure due to international data privacy laws.
The rollout of the European Union’s General Data Protection Regulation (GDPR) fundamentally altered global data processing. Because the GDPR carries severe financial penalties (up to €20 million or 4% of global turnover), it forces international companies to heavily audit their data flows.
For many small to medium-sized enterprises and regional publishers based in the US or Asia, the cost of auditing data, hiring Data Protection Officers, and risking devastating fines far outweighs the value of incidental web traffic from Europe.
As a result, thousands of legitimate sites deploy preemptive server-side geoblocking. They automatically serve a standard HTTP 451 (Unavailable For Legal Reasons) error code to any IP address originating from the EU. This trend is accelerating globally with the implementation of strict data localization laws in India (DPDPA), Vietnam, and various US states.
If your website relies on standard infrastructure configurations that automatically enforce geographic compliance and data sovereignty, you might need a comprehensive site structure optimization to ensure legitimate users from strictly regulated regions aren't blocked at the server level just to mitigate corporate risk.
3. The Protocol Arms Race: How Upgrading Security Gets You Blocked
There is a fascinating and highly destructive arms race occurring between global privacy advocates and state censors, and your website might be caught in the middle simply because you upgraded your security.
Historically, authoritarian regimes used Deep Packet Inspection (DPI) to monitor unencrypted Server Name Indication (SNI) data during a user's connection request, allowing them to block specific dissenting websites while leaving the rest of the web untouched.
To close this privacy loophole, the internet engineering community introduced TLS 1.3 and Encrypted Client Hello (ECH), which encrypt the entire handshake process. Because national firewalls (like China's Great Firewall or Russia's Roskomnadzor) can no longer read the destination domain name within the encrypted traffic, they face a binary choice: allow all traffic, or drop the connection entirely.
They often choose the latter. In recent years, both China and Russia have deployed updates to their firewalls to systematically drop traffic utilizing TLS 1.3 and ECH. If your site uses a major CDN that enables these modern encryption protocols by default, your content will be instantly blocked in these regions - not because of what you published, but because your connection is too secure for the state to monitor.
4. Overzealous Web Application Firewalls (WAF) and Anomaly Scoring
If your site is suddenly inaccessible to a cluster of corporate users or a specific geographic demographic, the culprit is often your own Web Application Firewall (WAF) generating false positives.
Enterprise firewalls provided by AWS, Microsoft Azure, and Cloudflare use anomaly scoring algorithms to protect against DDoS attacks and bot scraping. These managed rule sets (like the OWASP Core Rule Set) are intentionally designed to be exceedingly strict out of the box.
Legitimate user behaviors frequently trip these thresholds:
- Non-Browser Agents: AWS WAF Bot Control routinely blocks traffic from custom mobile apps or legacy browsers prevalent in specific developing regions.
- False Attack Signatures: A user submitting a standard form containing formatting that vaguely resembles code (e.g., the string 1=1) might trigger an Azure SQL Injection rule (Rule 942130), resulting in a silent block.
BGP ASN Blackholing: To stop scraping, security administrators often ban entire Autonomous System Numbers (ASNs) associated with certain internet service providers. If a legitimate user accesses your site via a corporate VPN or an ISP that shares an ASN with bad actors, they are locked out.
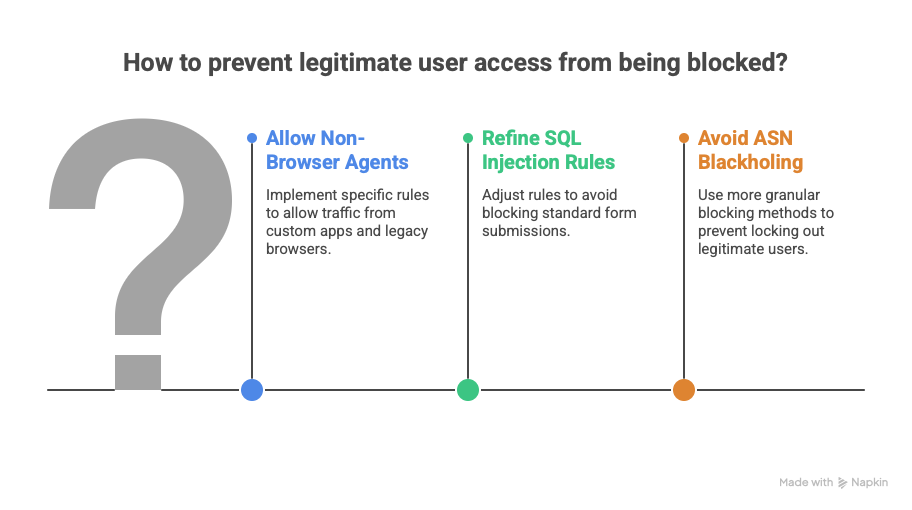
Properly configuring your WAF by refining rules and avoiding broad ASN blackholing is crucial to maintaining global accessibility.
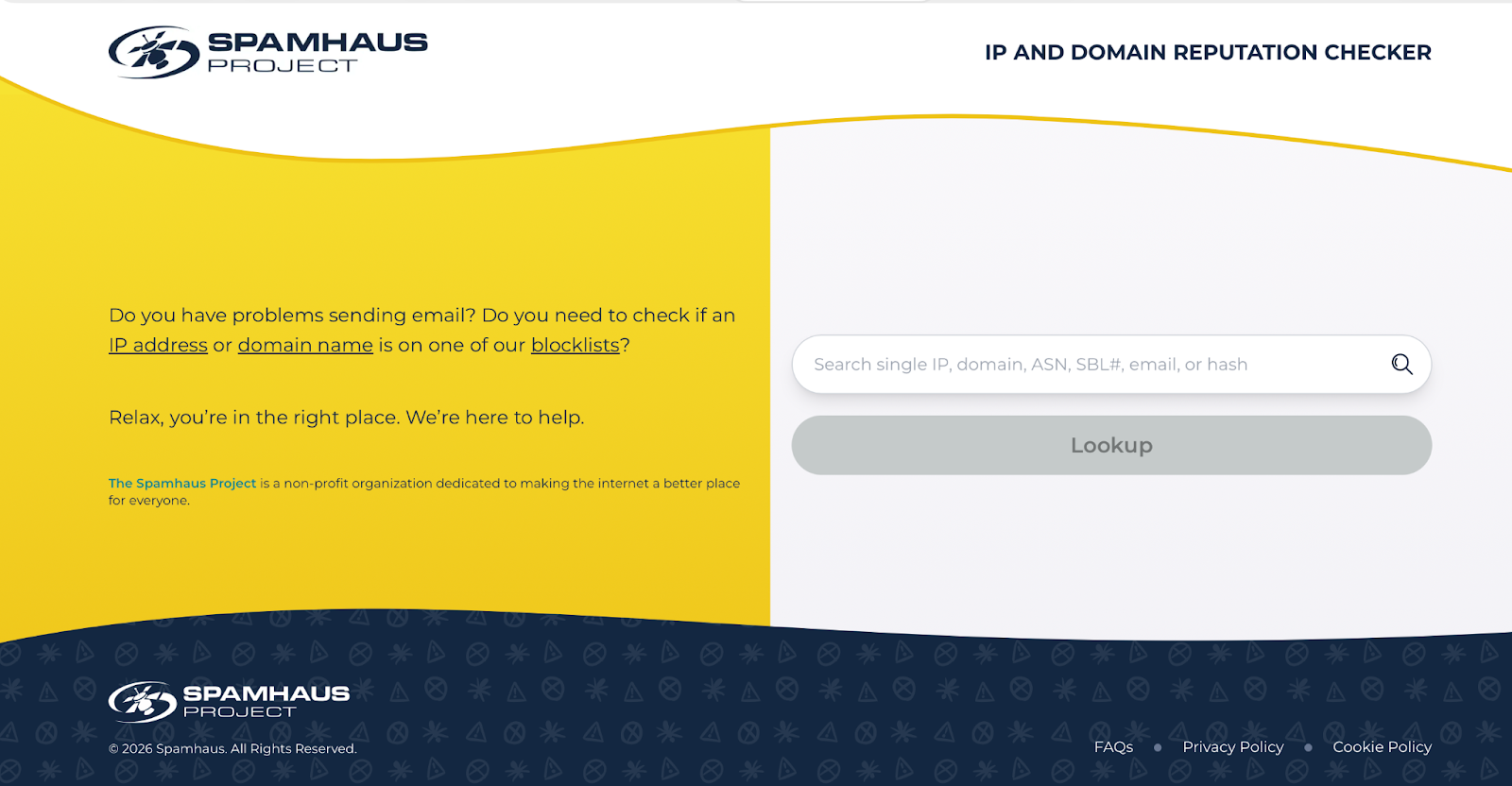
Even essential tools, like automated compliance scanners verifying website accessibility or crawlers utilizing modern sitemaps in practice, are frequently flagged as malicious scrapers by aggressive IP reputation blacklists like the Spamhaus Blocklist (SBL), cutting off your ability to perform critical site audits.
5. Invisible Glitches: BGP Leaks and SSL Misconfigurations
Finally, regional blocking is often a symptom of deep structural failures in the internet's core routing architecture.
- BGP Route Leaks: The Border Gateway Protocol (BGP) dictates how traffic physically moves across the globe. Because it relies on trust, misconfigurations are common. A single automated routing error at a major data center can cause massive volumes of global internet traffic to be drawn into hardware not provisioned for it, resulting in localized traffic drops (such as the highly disruptive Cloudflare route leak incident in Miami). Users in Brazil might lose access to your site for hours while users in London see no issues.
- Incomplete SSL Certificate Chains: If your hosting server fails to transmit intermediate certificates during the secure handshake, modern browsers might dynamically fetch them, but older, legacy mobile devices (highly prevalent in developing regions) will fail the handshake entirely. To the end-user, this appears as an impenetrable regional block.
- CDN Point-of-Presence (PoP) Failures: If a specific regional CDN node in Frankfurt experiences hardware failure, users routed to that node will face timeouts, while users in Asia connecting to a Tokyo node experience flawless load times. Keep in mind that speed is the new currency; a slow, misconfigured CDN node can act exactly like an intentional regional block.
How to Diagnose and Resolve Non-Punitive Regional Blocks
Resolving these issues requires moving beyond basic server metrics and looking at the web from the outside in. Here is the operational checklist:
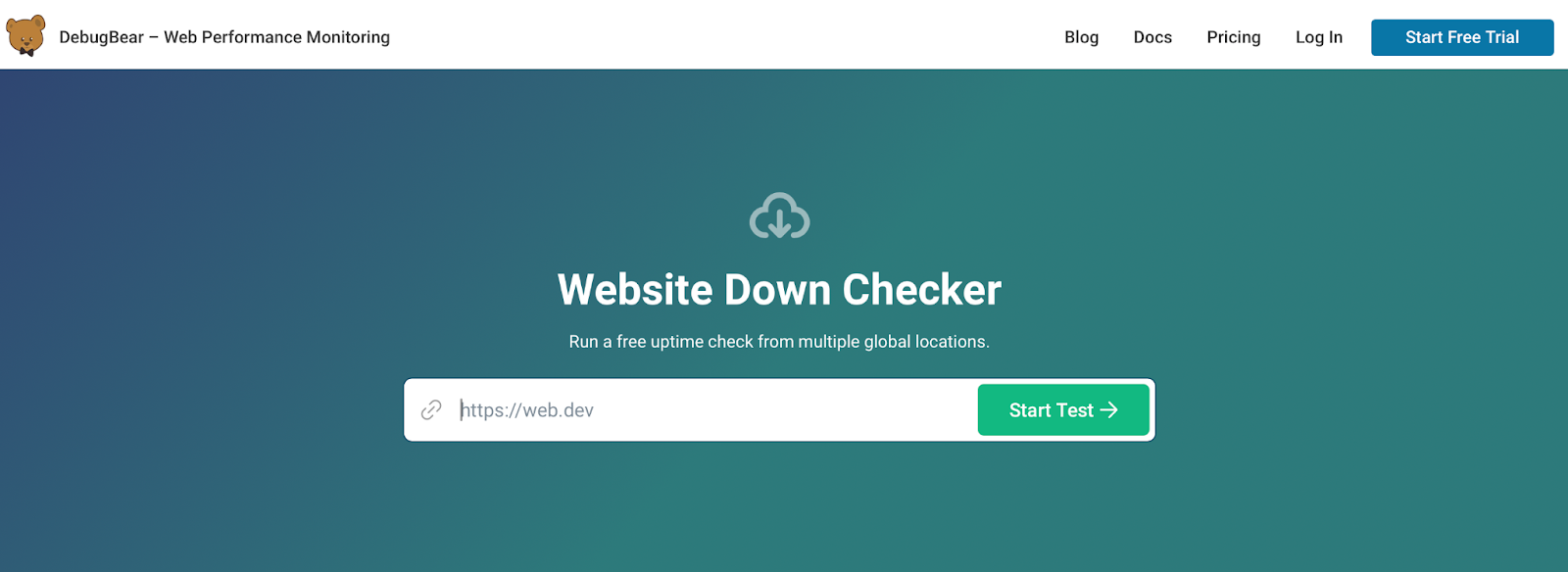
Deploy Synthetic Global Monitoring: Standard uptime tools ping your server from one location. You must use tools like DebugBear, Check-Host, or Semonto to test reachability, HTTP status codes, and SSL handshakes simultaneously from dozens of different global vantage points.
Audit Your WAF Logs: Dive deep into your Azure or AWS firewall logs. Look for the specific transaction IDs and rule triggers (e.g., details.data). Create highly granular exclusion lists rather than globally disabling essential security rules.
Evaluate Multi-CDN Architectures: Relying on a single CDN creates a single point of failure. Implementing a multi-CDN strategy ensures that if one provider faces an IP blacklist in Italy or a BGP routing leak in Miami, traffic seamlessly fails over to a healthy network.
Review Protocol Compatibility: If you are losing traffic in specific developing nations, audit your SSL/TLS configurations. Additionally, check if complex routing rules based on your structure are triggering legacy WAF rules. Ensure your certificate chains are complete and assess whether strictly enforcing TLS 1.3 is prematurely alienating users on legacy hardware.
Check Global IP Reputation: Regularly verify your server IP addresses against databases like Spamhaus, Cisco Talos, and Microsoft SmartScreen. If your shared IP is blacklisted due to a previous tenant, you must initiate the manual delisting process immediately.
The assumption that an inaccessible website is the result of targeted, punitive action is a misunderstanding of the modern internet's fragility. By understanding the architectural, legal, and cryptographic fault lines that divide the web, you can ensure your content remains truly global.
Are you struggling with unexplained traffic drops or complex technical SEO issues? Discover the top 10 reasons why your site might be invisible on Google and learn how to resolve them today.




